Installing an Agent
System Requirements
| Name | Value |
|---|---|
| Minimum RAM | 500 MB |
| Recommended RAM | 1GB |
| Supported Operating System Types | 64 bit |
| Supported Windows Server Versions | 2008 R2 SP1 & later |
| Support Linux Variants | View Here |
Currently the Loome Integrate Online Agent does not support proxies and so proxies must be disabled during the installation process.
Download Installer
The Agent installer is a single Powershell Script that will download the necessary run times, the newest version of the agent and it will also pre-configure your agent to connect to this tenant.
The install script will automatically be installed as a Local System account. To change the account settings, you will need to modify the service. (You can read about modifying the service in the next section.)
Once you’ve downloaded the script, make sure to run the script with administrator privileges.
Windows users will need to ensure they have Powershell 4 at a minimum installed.
Linux users will need to install Powershell Core for their platform.
Run the Installer
Navigating to the Agent Installer in Loome Integrate Online
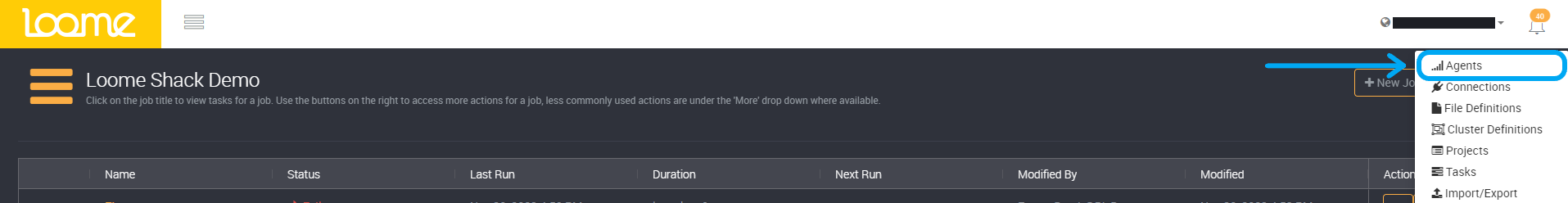
From the homepage, click on the Tenant name in the top-right corner. From the resulting dropdown menu, select Agents.
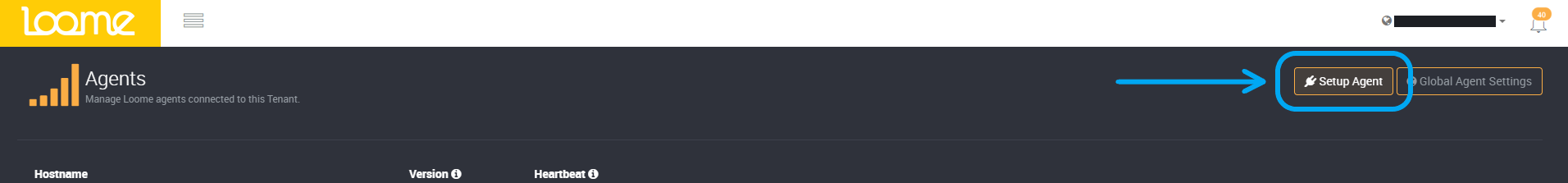
On the Agents page, select Setup Agent.
You can then follow the prompts in the installation wizard for your chosen platform.
Click on ‘Next Steps …’ for your platform.
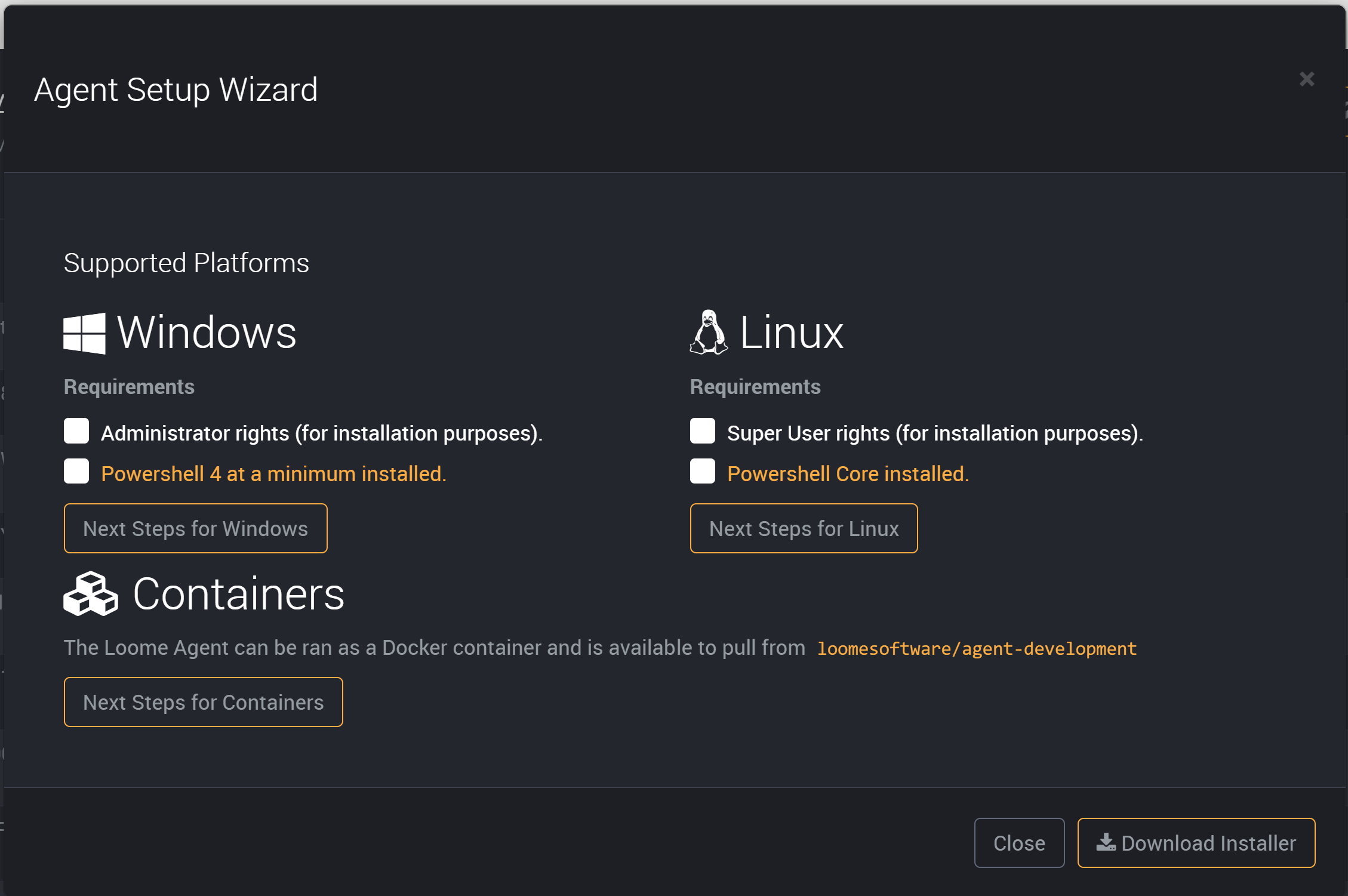
The next example is in Windows, and the following sections contain more information for other platforms.
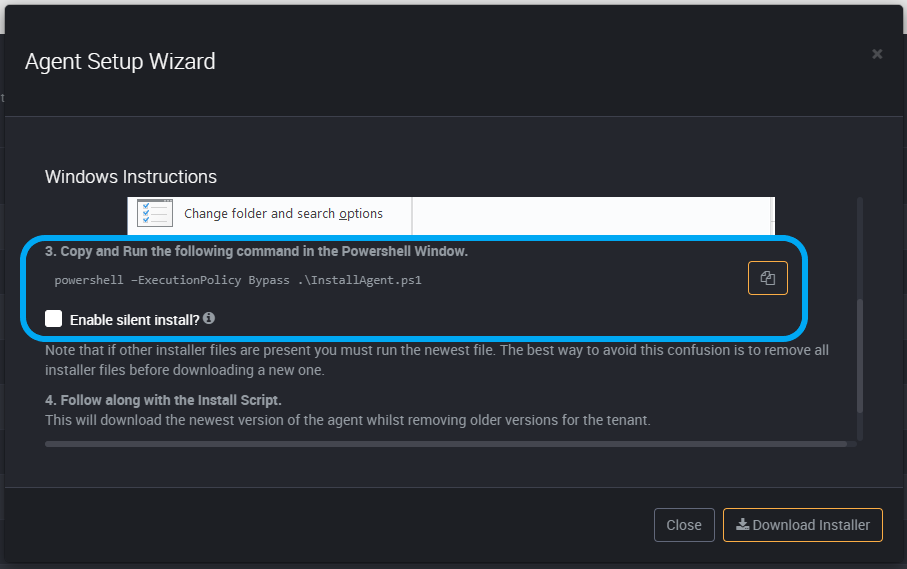
Open PowerShell as an Administrator in the folder that contains the new Loome agent installer.
Copy and run the command, which you can copy from Loome once you have chosen a platform, into your (Administrator) PowerShell Window.
If other Loome agent installer files are present in this folder, you must run the newest file. The best way to avoid any confusion is to remove all installer files before downloading a new agent.
Linux
Open an elevated shell, and then run PowerShell Core.
Copy and run the command from Loome.
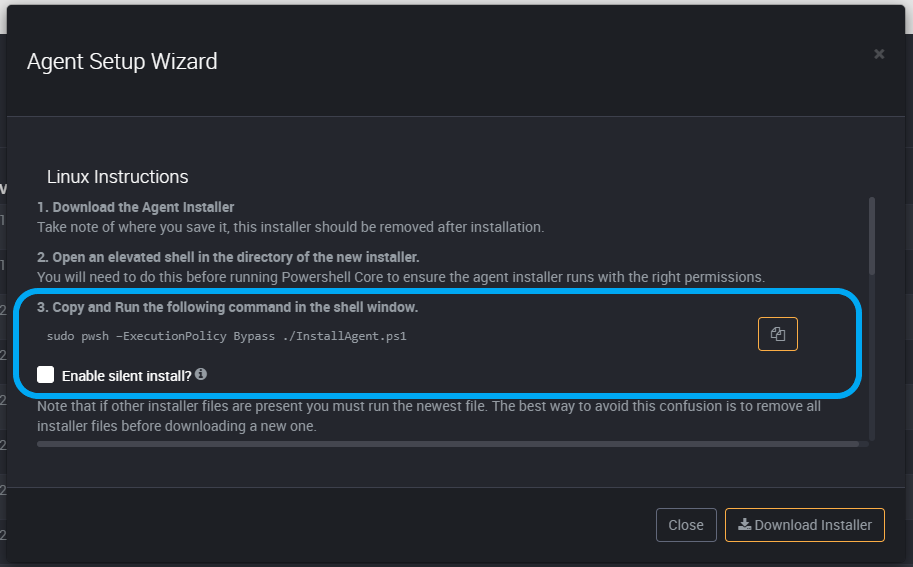
Silent Install
You can also use the script with the silent install option. It will proceed with the agent installation by selecting the default options for the prompts. It will choose “Y” for confirming the installation of the agent, “N” for installing SnowSQL (for use with Snowflake Cloud Data Warehouse), and “N” for using Microsoft Genomics.
To use silent install, select the checkbox beneath the install script.
Copy the script and paste it into your installation window, Administrator PowerShell, and run the script.
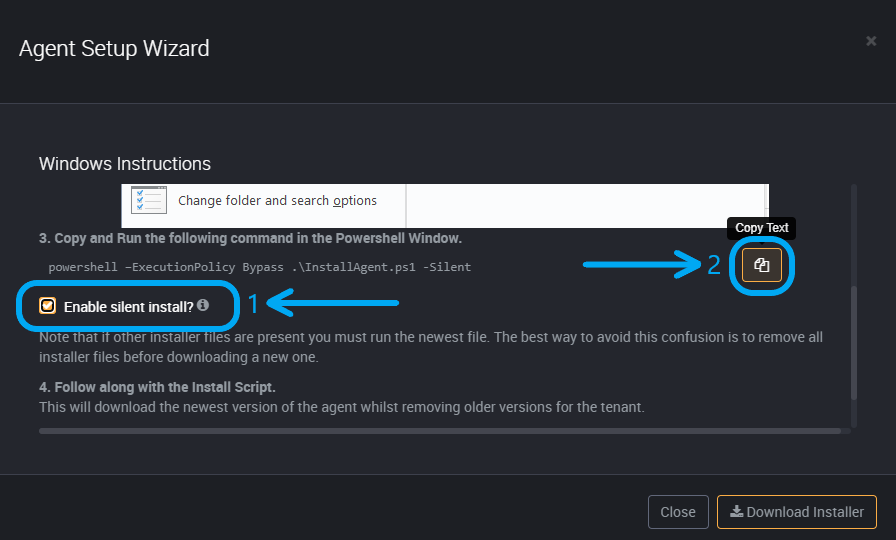
This will download the newest version of the agent whilst removing older versions for the tenant.
It will start the service and complete installation.
You are then ready to use this agent.
If you see that the agent is unhealthy in Loome Integrate, first refresh the page and if it is still unhealthy please restart the service.
Modifying the Service
First, open up Services on your computer.
Find the agent you just installed with the same name listed in Services. It will be loome-agent followed by your unique agent code.
Once you’ve found your agent, open up the log on window.
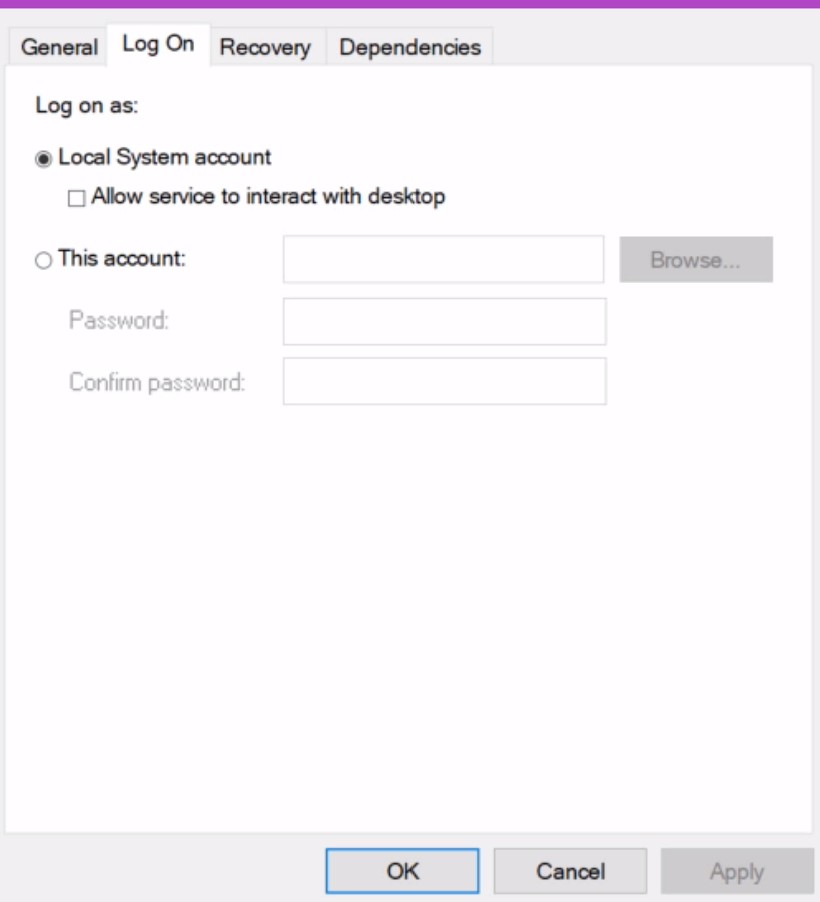
Change the account here.
Once you save, the agent will now use this account.
Installation Locations
Loome Integrate Agents are installed in a standard directory, based on a unique ID. All agent installs can be found in %ProgramData%\LoomeAgent on Windows and /.loomeagent/ on Linux. There is no need to take note of this directory when updating the agent, as the install script will automatically detect if an agent is installed for the related tenant.
Running Without a Service
Whilst we highly recommend you run the agent as a service, you are able to run it as a console application you startup when necessary. Agents can be run as a console application using the Run.ps1 powershell script located in their install directory.
Windows Considerations
If the agent is running as a service, you will need to provide an account with “Logon as a Service” functionality.
When providing the username and password credentials for the service, ensure that you include the domain as part of the username. Eg: “Company\User” or “DeviceName\LocalUser”
Agent services can be viewed in the Windows Services manager under the name loome-agent-[unique identifier for the agent] (eg:loome-agent-b0...-f6e78).
Linux Considerations
“loomeusers” Group
The installer will create a new group called loomeusers on install, this group is used for managing file permissions in the /.loomeagent directory and so it is a requirement that the group is created.
Installing the Agent as a Container
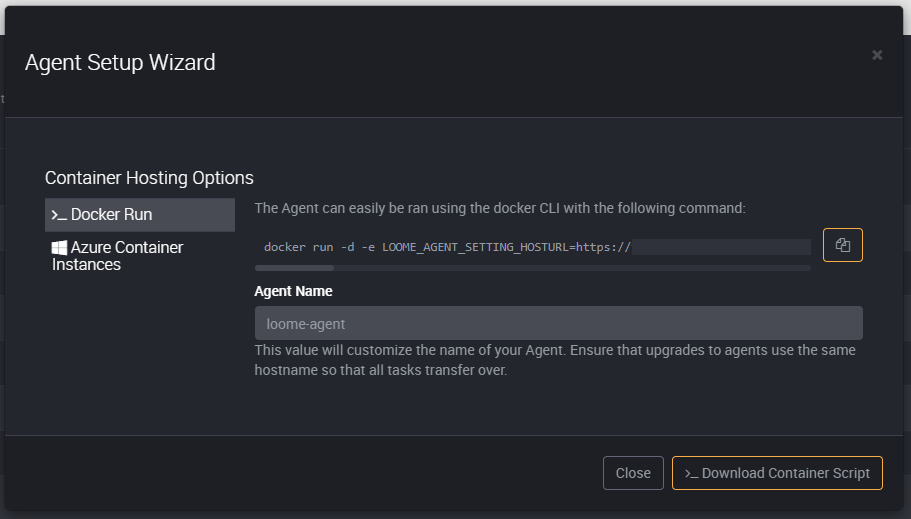
Loome Integrate also supports running the agent using Docker. The official Loome Integrate Agent image is available from the Docker Hub at loomesoftware/agent. Docker Agents are configured entirely through environment variables/secrets so there is no need to mount additional volumes for configuration files. Using the Docker installation screen, you can generate shell commands that will pre-configure the Docker based agent to automatically run and connect to your tenancy.
Once installed, this Docker agent will include PowerShell 7.
To update agents being hosted in Docker, just run the same installation script again.
Whilst Loome Integrate only generates commands for certain installation options, the agent is compatible with any Docker based platform.
Using Docker Run
The Docker Run tab provides a generated command for installing the agent using docker run. This command by default will run the
agent as a detached background service which will automatically restart with the host PC’s restart.
Whilst the Docker Run command provides all environment variables inline with the -e switch, these environment variables can be
used to host the agent using other means such as an envlist or orchestration engines like Docker Swarm and Kubernetes.
Using Azure Container Instances
The Azure Container Instances (ACI) tab provides a generated command for create an ACI resource for the agent.
The command provided needs to be ran in an instance of the Azure Cloud Shell or a connected Azure CLI, a valid resource group name is also required for billing purposes.
SQL Server may require a firewall exception for the container. To get a containers public IP address, execute the following command in the Azure Container instance: curl ifconfig.co